Mac Flooding In Ethical Hacking
Download PDF
- Ethical Hacking Example
- Mac Flooding In Ethical Hacking Software
- Ethical Hacking Pdf
- Mac Flooding In Ethical Hacking 2016
1) Explain what is Ethical Hacking?
Ethical Hacking is when a person is allowed to hacks the system with the permission of the product owner to find weakness in a system and later fix them.
This Ethical Hacking Interview Questions and answers are prepared by Ethical Hacking Professionals based on MNC Companies expectation. Stay tuned we will update New Ethical Hacking Interview questions with Answers Frequently. Mac Flooding is a technique of where the security of given to network switch is compromised. In Mac flooding the. Ethical Hacking is a technique of locating weakness and vulnerabilities of a network and the computer systems connected to that network. These hacking skills are used for defensive purpose on behalf of the owner of the information system. MAC FLOODING Mac Of Document. MAC Flooding is one of the most common network attacks. Unlike other web attacks, MAC Flooding is not a method of attacking any host machine in the network, but it is the method of attacking the network switches. MAC Flooding MAC Flooding is one of the most common network attacks. Unlike other web attacks, MAC Flooding is not a method of attacking any host machine in the network, but it is the method of attacking the network switches. However, the victim of the attack is a host computer in the network. We are going to see what the MAC Flooding is and how can we prevent it.
2) What is the difference between IP address and Mac address?
Jun 01, 2019 To keep it short - Switch is flooded with random packets with random source MAC address, so as to overflow the switch MAC table and the original entries of the MAC table will be removed. So now when a switch receives a packet, instead of sending i.
IP address: To every device IP address is assigned, so that device can be located on the network. In other words IP address is like your postal address, where anyone who knows your postal address can send you a letter.

MAC (Machine Access Control) address: A MAC address is a unique serial number assigned to every network interface on every device. Mac address is like your physical mail box, only your postal carrier (network router) can identify it and you can change it by getting a new mailbox (network card) at any time and slapping your name (IP address) on it.
3) List out some of the common tools used by Ethical hackers?

- Meta Sploit
- Wire Shark
- NMAP
- John The Ripper
- Maltego
4) What are the types of ethical hackers?
The types of ethical hackers are
- Grey Box hackers or Cyberwarrior
- Black Box penetration Testers
- White Box penetration Testers
- Certified Ethical hacker
5) What is footprinting in ethical hacking? What is the techniques used for footprinting?
Footprinting refers accumulating and uncovering as much as information about the target network before gaining access into any network. The approach adopted by hackers before hacking
- Open Source Footprinting : It will look for the contact information of administrators that will be used in guessing the password in Social engineering
- Network Enumeration : The hacker tries to identify the domain names and the network blocks of the target network
- Scanning : Once the network is known, the second step is to spy the active IP addresses on the network. For identifying active IP addresses (ICMP) Internet Control Message Protocol is an active IP addresses
- Stack Fingerprinting : Once the hosts and port have been mapped by scanning the network, the final footprinting step can be performed. This is called Stack fingerprinting.
6) Explain what is Brute Force Hack?
Brute force hack is a technique for hacking password and get access to system and network resources, it takes much time, it needs a hacker to learn about JavaScripts. For this purpose, one can use tool name “Hydra”.
7) Explain what is DOS (Denial of service) attack? What are the common forms of DOS attack?
Denial of Service, is a malicious attack on network that is done by flooding the network with useless traffic. Although, DOS does not cause any theft of information or security breach, it can cost the website owner a great deal of money and time.
- Buffer Overflow Attacks
- SYN Attack
- Teardrop Attack
- Smurf Attack
- Viruses
8) Explain what is SQL injection?
SQL is one of the technique used to steal data from organizations, it is a fault created in the application code. SQL injection happens when you inject the content into a SQL query string and the result mode content into a SQL query string, and the result modifies the syntax of your query in ways you did not intend.
9) What are the types of computer based social engineering attacks? Explain what is Phishing?
Computer based social engineering attacks are
- Phishing
- Baiting
- On-line scams
Phishing technique involves sending false e-mails, chats or website to impersonate real system with aim of stealing information from original website.
10) Explain what is Network Sniffing?
A network sniffer monitors data flowing over computer network links. By allowing you to capture and view the packet level data on your network, sniffer tool can help you to locate network problems. Sniffers can be used for both stealing information off a network and also for legitimate network management.
11) Explain what is ARP Spoofing or ARP poisoning?
ARP (Address Resolution Protocol) is a form of attack in which an attacker changes MAC ( Media Access Control) address and attacks an internet LAN by changing the target computer’s ARP cache with a forged ARP request and reply packets.
12) How you can avoid or prevent ARP poisoning?
ARP poisoning can be prevented by following methods
- Packet Filtering : Packet filters are capable for filtering out and blocking packets with conflicting source address information
- Avoid trust relationship : Organization should develop protocol that rely on trust relationship as little as possible
- Use ARP spoofing detection software : There are programs that inspects and certifies data before it is transmitted and blocks data that is spoofed
- Use cryptographic network protocols : By using secure communications protocols like TLS, SSH, HTTP secure prevents ARP spoofing attack by encrypting data prior to transmission and authenticating data when it is received
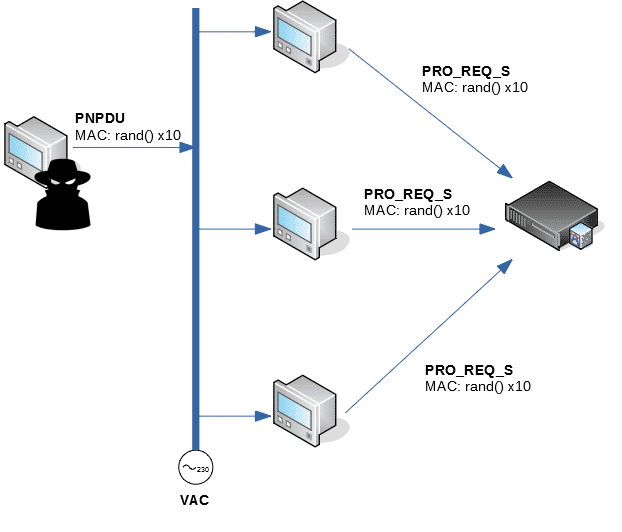
13) What is Mac Flooding?
Mac Flooding is a technique where the security of given network switch is compromised. In Mac flooding the hacker or attacker floods the switch with large number of frames, then what a switch can handle. This make switch behaving as a hub and transmits all packets at all the ports. Taking the advantage of this the attacker will try to send his packet inside the network to steal the sensitive information.
14) Explain what is DHCP Rogue Server?
A Rogue DHCP server is DHCP server on a network which is not under the control of administration of network staff. Rogue DHCP Server can be a router or modem. It will offer users IP addresses , default gateway, WINS servers as soon as user’s logged in. Rogue server can sniff into all the traffic sent by client to all other networks.
15) Explain what is Cross-site scripting and what are the types of Cross site scripting?
Cross site scripting is done by using the known vulnerabilities like web based applications, their servers or plug-ins users rely upon. Exploiting one of these by inserting malicious coding into a link which appears to be a trustworthy source. When users click on this link the malicious code will run as a part of the client’s web request and execute on the user’s computer, allowing attacker to steal information.
There are three types of Cross-site scripting
- Non-persistent
- Persistent
- Server side versus DOM based vulnerabilities
16) Explain what is Burp Suite, what are the tools it consist of?
Burp suite is an integrated platform used for attacking web applications. It consists of all the Burp tools required for attacking an application. Burp Suite tool has same approach for attacking web applications like framework for handling HTTP request, upstream proxies, alerting, logging and so on.
The tools that Burp Suite has
- Proxy
- Spider
- Scanner
- Intruder
- Repeater
- Decoder
- Comparer
- Sequencer
17) Explain what is Pharming and Defacement?
- Pharming: In this technique the attacker compromises the DNS ( Domain Name System) servers or on the user computer so that traffic is directed to a malicious site
- Defacement: In this technique the attacker replaces the organization website with a different page. It contains the hackers name, images and may even include messages and background music
18) Explain how you can stop your website getting hacked?
By adapting following method you can stop your website from getting hacked
- Sanitizing and Validating users parameters: By Sanitizing and Validating user parameters before submitting them to the database can reduce the chances of being attacked by SQL injection
- Using Firewall: Firewall can be used to drop traffic from suspicious IP address if attack is a simple DOS
- Encrypting the Cookies: Cookie or Session poisoning can be prevented by encrypting the content of the cookies, associating cookies with the client IP address and timing out the cookies after some time
- Validating and Verifying user input : This approach is ready to prevent form tempering by verifying and validating the user input before processing it
- Validating and Sanitizing headers : This techniques is useful against cross site scripting or XSS, this technique includes validating and sanitizing headers, parameters passed via the URL, form parameters and hidden values to reduce XSS attacks
19) Explain what is Keylogger Trojan?
Keylogger Trojan is malicious software that can monitor your keystroke, logging them to a file and sending them off to remote attackers. When the desired behaviour is observed, it will record the keystroke and captures your login username and password.
20) Explain what is Enumeration?
The process of extracting machine name, user names, network resources, shares and services from a system. Under Intranet environment enumeration techniques are conducted.
21) Explain what is NTP?
To synchronize clocks of networked computers, NTP (Network Time Protocol) is used. For its primary means of communication UDP port 123 is used. Over the public internet NTP can maintain time to within 10 milliseconds
22) Explain what is MIB?
MIB ( Management Information Base ) is a virtual database. It contains all the formal description about the network objects that can be managed using SNMP. The MIB database is hierarchical and in MIB each managed objects is addressed through object identifiers (OID).
23) Mention what are the types of password cracking techniques?
The types of password cracking technique includes
- AttackBrute Forcing
- AttacksHybrid
- AttackSyllable
- AttackRule
24) Explain what are the types of hacking stages?
The types of hacking stages are
- Gaining AccessEscalating
- PrivilegesExecuting
- ApplicationsHiding
- FilesCovering Tracks
25) Explain what is CSRF (Cross Site Request Forgery)? How you can prevent this?
CSRF or Cross site request forgery is an attack from a malicious website that will send a request to a web application that a user is already authenticated against from a different website. To prevent CSRF you can append unpredictable challenge token to each request and associate them with user’s session. It will ensure the developer that the request received is from a valid source.
MAC spoofing is a technique for changing a factory-assigned Media Access Control (MAC) address of a network interface on a networked device. The MAC address that is hard-coded on a network interface controller (NIC) cannot be changed. However, many drivers allow the MAC address to be changed. Additionally, there are tools which can make an operating system believe that the NIC has the MAC address of a user's choosing. The process of masking a MAC address is known as MAC spoofing. Essentially, MAC spoofing entails changing a computer's identity, for any reason, and it is relatively easy.[1]
Motivation[edit]
The changing of the assigned MAC address may allow the bypassing of access control lists on servers or routers, either hiding a computer on a network or allowing it to impersonate another network device. MAC spoofing is done for legitimate and illicit purposes alike.
Ethical Hacking Example
New hardware for existing Internet Service Providers (ISP)[edit]
Many ISPs register the client's MAC address for service and billing services.[2] Since MAC addresses are unique and hard-coded on network interface controller (NIC) cards,[1] when the client wants to connect a new gadget or change their existing gadget, the ISP will detect different MAC addresses and the ISP might not grant Internet access to those new devices. This can be circumvented easily by MAC spoofing. The client only needs to spoof the new device's MAC address to the MAC address that was registered by the ISP.[2] In this case, the client spoofs their MAC address to gain Internet access from multiple devices. While this seems like a legitimate case, MAC spoofing new gadgets can be considered illegal if the ISP's user-agreement prevents the user from connecting more than one device to their service. Moreover, the client is not the only person who can spoof their MAC address to gain access to the ISP. Hackers can gain unauthorized access to the ISP via the same technique. This allows hackers to gain access to unauthorized services, and the hacker will be hard to identify because the hacker uses the client's identity. This action is considered an illegitimate use of MAC spoofing and illegal as well. However, it is very hard to track hackers that are utilizing MAC spoofing.[3]
This also applies to customer-premises equipment, such as cable and DSL modems. In cases where the provider leases the equipment to the customer on a monthly basis, the CPE has a hard-coded MAC address which is on a list known to the provider's distribution networks, allowing service to be established as long as the customer is not in billing arrears. In cases where the provider allows customers to provide their own equipment (and thus avoid the monthly leasing fee on their bill,) the provider requires that the customer give them the MAC address of their equipment before service will be established.
Fulfilling software requirements[edit]
Some software can only be installed and run on systems with pre-defined MAC addresses as stated in the software end-user license agreement, and users have to comply with this requirement in order to gain access to the software. If the user has to install different hardware due to malfunction of the original device or if there is a problem with the user's NIC card, then the software will not recognize the new hardware. However, this problem can be solved using MAC spoofing. The user just has to spoof the new MAC address as to mimic the MAC address that was registered by the software.[citation needed] This activity is very hard to define as either legitimate or illegitimate reason for MAC spoofing. Legal issues might arise if the user grants access to the software on multiple devices simultaneously. At the same time, the user can obtain access to software for which he or she has not secured a license. Contacting the software vendor might be the safest route to take if there is a hardware problem preventing access to the software. Software may also perform MAC filtering because the software does not want unauthorized users to gain access to certain networks to which the software grants access. In such cases MAC spoofing can be considered a serious illegal activity and can be legally punished.[4]
Identity masking[edit]
If a user chooses to spoof their MAC address in order to protect the user's privacy,[citation needed] this is called identity masking. One might wish to do this because, as an example, on a Wi-Fi network connection a MAC address is not encrypted. Even the secure IEEE 802.11i-2004 (WPA) encryption method does not prevent Wi-Fi networks from sending out MAC addresses.[citation needed] Hence, in order to avoid being tracked, the user might choose to spoof the device's MAC address. However, hackers use the same technique to maneuver around network permissions without revealing their identity. Some networks use MAC filtering in order to prevent unwanted access. Hackers can use MAC spoofing to get access to a particular network and do some damage. Hackers' MAC spoofing pushes the responsibility for any illegal activity onto authentic users. As a result, the real offender may go undetected by law enforcement.[citation needed]
MAC Address Randomization in WiFi[edit]
To prevent third parties from using the MAC address to track devices, Android, Linux, iOS, and Windows[5] have implemented MAC addressrandomization. In June 2014, Apple announced that future versions of their iOS platform would randomize MAC addresses for all WiFi connections. The Linux kernel has supported MAC address randomization during network scans since March 2015,[6] but drivers need to be updated to use this feature.[7] Windows has supported it since the release of Windows 10[5] in July 2015.
Controversy[edit]
Although MAC address spoofing is not illegal, its practice has caused controversy in some cases. In the 2012 indictment against Aaron Swartz Internet hacktivist, who was accused of illegally accessing files from JSTOR digital library, prosecutors claimed that because he had spoofed his MAC address it showed purposeful intent to commit criminal acts.[4] In June 2014, Apple announced that future versions of their iOS platform would randomize MAC addresses for all WiFi connections, making it more difficult for internet service providers to track user activities and identities, which resurrected moral and legal arguments surrounding the practice of MAC spoofing among several blogs and newspapers.[8]
Limitations[edit]
MAC address spoofing is limited to the local broadcast domain. Unlike IP address spoofing, where senders spoof their IP address in order to cause the receiver to send the response elsewhere, in MAC address spoofing the response is usually received by the spoofing party if switch is not configured to prevent MAC spoofing.
See also[edit]
- ifconfig, linux utility capable of changing MAC address
Mac Flooding In Ethical Hacking Software
References[edit]
Ethical Hacking Pdf
- ^ abCardenas, Edgar D. 'MAC Spoofing--An Introduction'. GIAC Security Essentials Certification. SANS Institute. Retrieved 8 February 2013.
- ^ ab'MAC Spoofing'. Royal Canadian Mounted Police. Research and Development Section in Collaboration with the NCECC’s Technology Unit. Archived from the original on 23 June 2012. Retrieved 8 February 2013.
- ^Gupta, Deepak; Gaurav Tiwari (4 November 2009). 'MAC SPOOFING AND ITS COUNTERMEASURES'(PDF). International Journal of Recent Trends in Engineering. 2 (4): 21. Retrieved 8 February 2013.
- ^ abIndictment against Aaron Swartz
- ^ abhttp://papers.mathyvanhoef.com/asiaccs2016.pdf
- ^https://w1.fi/cgit/hostap/plain/wpa_supplicant/ChangeLog
- ^https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=ad2b26abc157460ca6fac1a53a2bfeade283adfa
- ^Change MAC Address: Use Public WiFi Signals Without Any Limits, Not To Mention Serious Privacy Benefits