Hacker Randomized Mac Address
Nov 19, 2019 MAC address filtering adds an extra layer to this process. Before letting any device join the network, the router checks the device's MAC address against a list of approved addresses. If the client's address matches one on the router's list, access is. Jan 30, 2019 By entering this -r option we can generate a random MAC for us lets see what MAC address i have got. Now we can resart our net connection by typing. Ifconfig eth0 up; After This, Lets check our current MAC address if its changed or not. Type this in terminal to check the MAC address. Macchanger -s eth0; Look our MAC address has ben changed. Dec 29, 2018 Right away you see a text input field with two buttons below it. One of the buttons says Generate random MAC while the other says Apply new MAC. Input the new MAC address in the text field and tap on Apply new MAC or tap on the Generate random MAC button if you want a random MAC address. Aug 09, 2018 Step 3: Find MAC (Media Access Control) address from the victim’s phone. A MAC address located in the device is basically a 12-character unique identifier given to your mobile device which acts as your mobile’s online identity.; Every Device has its own unique MAC address. A MAC Address includes six pairs of digits which are separated by colons. Technically, it would be next to impossible to trace back a random MAC address to an individual. Notwithstanding the fact that MAC addresses can easily be spoofed or changed (which means that your defender has bad opsec if they are using the default hardware MAC on the network), they are, at best, linked to a specific network card. In this article, we have presented how to hack IP addresses. If you followed our guide carefully, you have now a website you can use to hack IP addresses silently. You also know what to do with such addresses, and hackers do with them. Now it’s up to you! Go out there and practice this technique, but be always conscious of what you’re doing.
Maybe someone scared you claiming to know your IP address. On the other hand, you could be the one trying to scare a friend by getting his IP address. Or, maybe, you just want to hear the truth about hacking IP address. Look no further, because in this guide we will give you all the truth. We will explain you how to hack IP addresses by following this agenda:
- A quick introduction to what IP addresses are
- How to hack IP addresses
- How hackers find out an IP address
- What can a hacker do when he knows your IP address
After reading this guide, you will be able to find out the IP address of potentially anyone, silently.
Is this legal?
Under most circumstances, it is. Knowing someone’s IP address is part of a “normal” communication over the Internet, so there is no problem in doing that. However, if you use the IP address to violate someone else’s PC, you are committing a crime under many jurisdictions. We do not endorse such activity. Everything you read should be tried on systems you own and control personally. We are not responsible for your actions.
Furthermore, remember that this is not legal advice. We are IT guys, not lawyers. If you are looking for legal advice it’s better to call your attorney.
Before Hack IP addresses
Before we start hacking, we should spend a few words on IP addresses. In IT, and in hacking specifically, never do anything without knowing what you are doing. Indeed, this concept is important here. A lot of people talk about “hack IP addresses” without even knowing what an IP address is. This can lead to unjustified fear among the ones being hacked or exaggerated glory among those who hack. What “hack an IP address” really mean? What can you do with that? Now, we are going to demystify IP address hacking.
What is an IP address?
An IP address is nothing more than a numeric identifier. It identifies a PC, smartphone, or any other device in a network, like the Internet. You can think of it like a snail mail address. If I know your snail mail address I know where you are, and I can send you some letters. With an IP address, I can know (roughly) where your device is, and send you some Internet traffic.
In other words, you are identified by your IP address over the Internet. Typically, your Internet provider assigns a public IP address to your router in your house. When your devices in your home network want to send traffic over the Internet, they will use that public IP address (shared among all of them).
The communication over the Internet happens with packets. Each piece of data is put in a packet, you can think of it as a letter. On the envelope, you always write source and destination IP addresses. The Internet will take care of delivering the packet to the right destination. Now, as you can see, if you send traffic out you will write your IP as source IP. This is the only way the other part can know it, and send some traffic back.
Article continues below the advertisement
Do we really need to use our real IP address as source?
Of course! Imagine you want to download a movie, see a web page, or anything else you do over the Internet. You contact a third-party server, which sends you the content you requested. It needs to know where to send it, so it needs to know your IP.
Read more about IP addresses in this detailed article.
Am I in danger?
It depends, but in most cases, you aren’t. As from the paragraph above, knowing someone else’s IP is legitimate. You need it to send traffic back. What if your IP address ends up in the wrong hands? Just by knowing your IP address, nobody can harm you. However, they can start to scan your PC and see if you have vulnerabilities they can use to gain access to your data. We will get to that later.
How to find out someone’s IP address?
In the following section, we are going to cover an out-of-the-box technique. However, it relies on a simple principle: your victim needs to send you some traffic. If he does that, boom, you have his IP address. Your PC already learns such an IP address, but it doesn’t show it to you. We will see how to see it.
The Proven Way to Hack IP addresses
Some misconceptions and old techniques
The Internet is full of poor content about hacking IP addresses. You might read about hacking IP addresses with Skype and get excited about that, but since 2017 this is not possible anymore. So, for this article, we are going to use the best way to hack an IP address. We are going to use the only way that depends uniquely on you, not third-party services. Because of that, it will always work.
Furthermore, it is simple to apply and easy to use.
What’s behind our technique
The idea behind our technique is simple. You basically give your victim a link: they can open it with their mobile, PC, or any sort of device. On that link, they will see an image of your choice (we recommend using a fun one). However, your system will also track automatically their IP address and more information, like the browser they are using and their operating system.
While this happens, they will see the fun image and have a laugh about it. They have no way of knowing that you are tracking their IP address.
Step #1 – Register a website (for free!)
You want to give your victim a valid link to click, and it must be valid online. Therefore, we need to register a website. There are a lot of free services online to register a website, and among them, we have chosen x10 hosting. Go to their website and register a new account.
As a first thing, they will ask you to select a domain image. Use a credible one for the kind of images you want to share.
Continue with the registration and verify your email. Once you complete the process, you will end up on the homepage where you will have to create a website. Now you are going to say “Wait, I thought we already created that!”… well, sort of. Until now, we created the name. Now, we have to prepare the software running behind it.
Step #2 – Creating the website itself
The home will look like the one below. From there, just click the green Add Website button on the top right.
Randomized Mac Address Iphone
A quick wizard will open. From there, we have to tune a few items. Before everything else, select “Custom Website” website. Then, as a website name, write something that reminds the website, like its domain name. As the last thing, leave the address path empty. Then, click on Add Website.
Create the website, then select “Continue to my website” on the next page. Congratulation, we are almost there!
Step #3 – Download the IPFinder script
Now your website is ready. All we need to do is uploading the script that will take care of saving IP addresses and delivering the images to the user. Fortunately, you don’t need to write that script on your own: instead, we did it for you. It uses a PHP file, three HTAccess files, and two folders.
Our IPFinder script comes in a useful zip package that you can download for free by using the link below. Just click on it and download the zip file.
Now that you have it, don’t even unzip it. We will do that on the website directly: move on to the next step.
Step #4 – Upload the IPFinder Script
From the website pages, select the File Manager option. This will open a new window that looks similar to Explorer in Windows. A website is just a collection of files on a public server. With this File Manager, you can have a look at those files. To them, we need to add our script.
Once you are in the file manager, select Upload (1). This will open a new window, where you can click “Browse” and search for the file you downloaded. Select that compressed file (ipfinder.zip) and wait for the upload to complete. Then, close this window and click Reload (2) in the previous window.
Now you should see a new file in the list, right below “cgi-bin”. This is our zipped package containing IPFinder, and we just need to extract it.
Step #5 – Extract the IPFinder
Select the ipfinder.zip so that its background turns blue. Then, from the top menu, select Extract.
A new window will pop-up. Just click on Extract File(s) without changing anything. Then, wait for the process to finish, and, as soon as it does, click the Close button. You will have some more files and folders on your list. In case you don’t, just hit the Reload button as we did previously.
At this point, I recommend you to delete the ipfinder.zip file. You don’t need it anymore, as we have extracted its content. So, just click it and then click the delete button at the top. This step is not mandatory, but it is a good practice.
Step #6 – Adding images
Our IPFinder comes without images. However, it is a script that shows an image and logs the IP of the viewer. Therefore, you need to add your own images. So, find a jpeg image that you think would work for this purpose. At the moment, our script only supports JPEG/JPG images. Once you have that image, rename it with a simple name without spaces. Then, double-click on the images folder to view its content.
Once you are in, you will see only a .htaccess file. That’s OK, now upload the image the same way we uploaded the IPFinder script. For example, we will be using an image named meme.jpg. Now click “Up One Level” to return to the main folder.
Step 7# – Using IPFinder
Now your IPFinder is ready to go. How do we use it? It is very simple, as it automatically creates the URL we need. Your URL to share with your victims will be something like this one.
In this URL, each part is customizable.
- The domain name is the name of your website, the one you selected when you created the account. You won’t be able to change this. In our case, this is “coolimages”.
- The image name is the name of the picture you uploaded, so in our case, this is “meme.jpg”
- The user ID is something you should select carefully. Here you can write any combination of letters and numbers you want. Now we will see how to use it
Selecting the User ID
IPFinder will save a new text file for each victim that sees the image in the log folder. That file contains the date, time, and the User ID you specify. The purpose of this field is to let you differentiate between users. Think about it, what if you want to give the link to multiple people? How can you know which IP corresponds to which person? You cant. With this approach, you would send to John the link to /meme.jpg/john and to Alice the link to /meme.jpg/alice. They will both see the same picture, but you will log their IPs separately.
Hack IP addresses, getting the results
Browse the log folder. You will see some text files with the names explained above. Open any of them and read their content (select it and click Edit). In each, you will see something like this.
Note that for privacy we have hidden some parts of the IP address and some parts of the browser info in this example. However, from your script, you will get the entire IP address and the full browser information.
What can you do with hacked IP addresses?
At this point, you have your IP finder in place. You shared some images, thus getting some IP. You can know truly hack IP addresses, but you are still wondering what can someone do with IP addresses. On the other hand, you might be the one who believes to be hacked, and you want to know if you are in real danger. Look no further, here we will tell you the ultimate truth about what happens after you hack IP addresses.
Hack IP addresses to scare people
A lot of self-proclaimed hackers hack IP addresses just to scare people. They contact the person and tell them they know their IP address, and maybe their browser. A normal PC user will believe they have accessed their PC, how would they know which browser they use otherwise? So, people get scared and start believing in the hacker.
I’ve heard stories about “hackers” who managed to extort money from someone with this approach. They basically make them believe they had access to their data and threatened to share some personal pictures or something like that. The truth is, they didn’t even know if those pictures really existed. However, they approached everyone with the same words. As a result, they would scare the hell out of anyone holding such kind of pictures. Of course, such activity is illegal.
Geolocating you
If you get someone’s IP address, you can geolocate it very approximately. The location will be a few square kilometers accurate in urban areas, and a few dozens square kilometers accurate in rural areas. This is a rule of thumb and might vary, but you will be never accurate enough.
Only your service provider, and thus the police, can locate you precisely with your home address. For the others, you need to get by with only knowing the city or county.
Hacker Randomized Mac Address Change
Truly gain access to the device or to personal data
If someone knows your IP address, he can scan you. This means he can try to detect the system you are running and your vulnerabilities. Now, since the public IP address of yours is on your home router, they will do that for your router. They will gain access to your router and, from that, they will adopt the same approach to gain access to your PC.
This process is long and complex and requires a skilled hacker. However, it always follows the same guidelines.
- Find exposed services (with nmap) and try to detect the hardware and software version with the TCP signature
- Look for common exploits on the exposed services, or for that specific hardware/software
- Try to gain access with brute force
- Try to create a custom exploit
Of course, the fourth step is so hard that many hackers will simply give up. That step if for someone with skills and budget that wants to hack specifically you.
How can I defend myself?
In many connections, rebooting your router will change your public IP address. That’s it. If a hacker was attacking you, they will have to find your IP again.
Furthermore, you can increase the level of security by using a VPN or a proxy chain like TOR. In this case, you basically contact a server you trust (maybe own) somewhere on the Internet. Then, that server makes requests on the web for you. In case someone tracks your IP address, they will track the IP address of that server. This is for a whole new article, however.
Conclusion
In this article, we have presented how to hack IP addresses. If you followed our guide carefully, you have now a website you can use to hack IP addresses silently. You also know what to do with such addresses, and hackers do with them. Now it’s up to you! Go out there and practice this technique, but be always conscious of what you’re doing.
What are your thoughts on hack IP addresses? Do you feel safe? Did you manage to scare a friend of yours? What would you like to learn after this? Just let me know in the comments!
Analysis To protect mobile devices from being tracked as they move through Wi-Fi-rich environments, there's a technique known as MAC address randomization. This replaces the number that uniquely identifies a device's wireless hardware with randomly generated values.
In theory, this prevents scumbags from tracking devices from network to network, and by extension the individuals using them, because the devices in question call out to these nearby networks using different hardware identifiers.
It's a real issue because stores can buy Wi-Fi equipment that logs smartphones' MAC addresses, so that shoppers are recognized by their handheld when they next walk in, or walk into affiliate shop with the same creepy system present. This could be used to alert assistants, or to follow people from department to department, store to store, and then sell that data to marketers and ad companies.
Public wireless hotspots can do the same. Transport for London in the UK, for instance, used these techniques to study Tube passengers.
Regularly changing a device's MAC address is supposed to defeat this tracking.
But it turns out to be completely worthless, due to a combination of implementation flaws and vulnerabilities. That and the fact that MAC address randomization is not enabled on the majority of Android phones.
In a paper published on Wednesday, US Naval Academy researchers report that they were able to 'track 100 per cent of devices using randomization, regardless of manufacturer, by exploiting a previously unknown flaw in the way existing wireless chipsets handle low-level control frames.'
Beyond this one vulnerability, an active RTS (Request to Send) attack, the researchers also identify several alternative deanonymization techniques that work against certain types of devices.
Cellular radio hardware has its own set of security and privacy issues; these are not considered in the Naval Academy study, which focuses on Android and iOS devices.
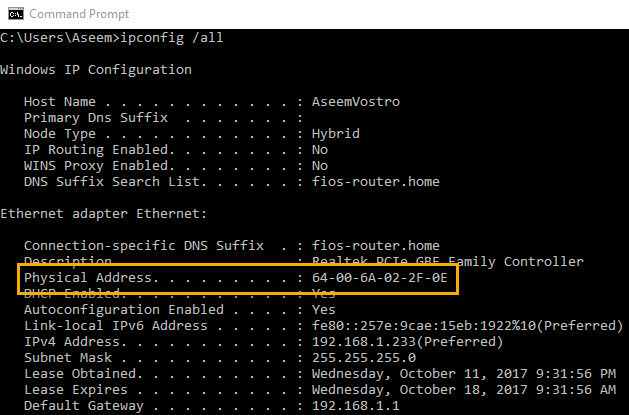
Each 802.11 network interface in a mobile phone has a 48-bit MAC addresslayer-2 hardware identifier, one that's supposed to be persistent and globally unique.
Hardware makers can register with the Institute of Electrical and Electronics Engineers (IEEE) to buy a block of MAC addresses for their networking products: the manufacturer is assigned a three-byte Organizationally Unique Identifier, or OUI, with is combined with an additional three-byte identifier that can be set to any value. Put those six bytes together, and you've got a 48-bit MAC address that should be globally unique for each device.
The IEEE's registration system makes it easy to identify the maker of a particular piece of network hardware. The IEEE also provides the ability to purchase a private OUI that's not associated with a company name, but according to the researchers 'this additional privacy feature is not currently used by any major manufacturers that we are aware of.'
Alternatively, the IEEE offers a Company Identifier, or CID, which is another three-byte prefix that can be combined with three additional bytes to form 48-bit MAC addresses. CID addresses can be used in situations where global uniqueness is not required. These CID numbers tend to be used for MAC address randomization and are usually transmitted when a device unassociated with a specific access point broadcasts 802.11 probe requests, the paper explains.
The researchers focused on devices unassociated with a network access point – as might happen when walking down the street through various Wi-Fi networks – rather than those associated and authenticated with a specific access point, where the privacy concerns differ and unique global MAC addresses come into play.
Unmasking
Previous security research has shown that flaws in the Wi-Fi Protected Setup (WPS) protocol can be used to reverse engineer a device's globally unique MAC address through a technique called Universally Unique IDentifier-Enrollee (UUID-E) reversal. The US Naval Academy study builds upon that work by focusing on randomized MAC address implementations.
The researchers found that 'the overwhelming majority of Android devices are not implementing the available randomization capabilities built into the Android OS,' which makes such Android devices trivial to track. It's not clear why this is the case, but the researchers speculate that 802.11 chipset and firmware incompatibilities might be part of it.